Data privacy has evolved significantly over the years, influenced by notable historical data breaches that have prompted both regulatory changes and advances in cybersecurity practices. Understanding the timeline of these events helps in grasping the contemporary landscape of data privacy.
The Early Days of Data Privacy
In the early days of computing, data was primarily stored on local systems, and the concept of data privacy was rudimentary. Organizations maintained limited data that was mostly peripheral to operations. The focus was not primarily on protecting this information; rather, it was assumed that computer systems were inherently secure due to their limited accessibility and the trust in local systems.
The Rise of the Internet and New Threats
With the advent of the internet in the 1990s, data sharing became more prevalent, introducing new vulnerabilities. As organizations began to connect to the web, the threat landscape expanded. Unauthorized access became a significant concern, leading to the first major data breaches and highlighting the need for robust cybersecurity measures.
Notable Historical Data Breaches
- Yahoo (2013 & 2014): One of the largest breaches in history, affecting over 3 billion accounts, this incident illustrated the consequences of inadequate security measures and poor handling of user data.
- Target (2013): This breach compromised the credit and debit card information of millions of customers due to malware installed on point-of-sale systems, emphasizing the vulnerability of retail operations.
- Equifax (2017): The personal data of approximately 147 million people was exposed, underscoring the risks associated with third-party data management and the importance of timely security updates.
Regulatory Responses and Frameworks
In response to increased data breaches, governments and organizations began establishing regulatory frameworks to enhance data privacy. Notable regulations include:
- Gramm-Leach-Bliley Act (GLBA): Enacted in the United States to protect consumers’ personal financial information held by financial institutions.
- Health Insurance Portability and Accountability Act (HIPAA): This act set standards for the protection of health information in the healthcare sector.
- General Data Protection Regulation (GDPR): A significant regulation in the European Union that sets guidelines for the collection and processing of personal data.
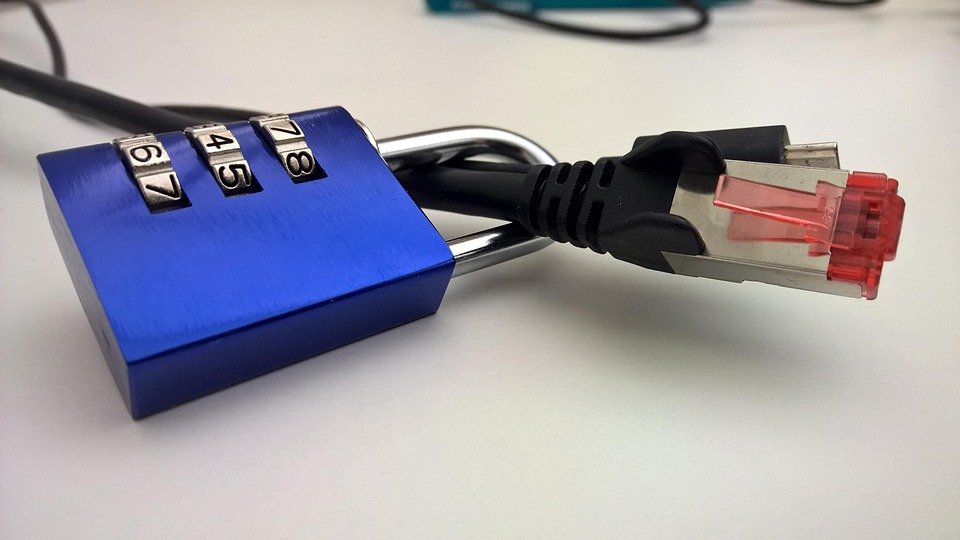
Advances in Cybersecurity Practices
The growing awareness of data privacy has led to the development of cybersecurity practices aimed at protecting sensitive information. These practices include:
- Data Encryption: Utilizing cryptography to secure data in transit and at rest, ensuring that unauthorized users cannot access it.
- Access Controls: Implementing strict access policies to ensure that only authorized personnel can access sensitive data.
- Incident Response Plans: Establishing protocols for responding to data breaches, thereby minimizing damage and restoring operations swiftly.
Conclusion
The evolution of data privacy is a reflection of the technological advancements and the accompanying threats that have emerged over the years. Learning from historical data breaches can provide valuable lessons for organizations, enabling them to implement better safeguards and foster a culture of data protection in an increasingly interconnected world. As technology continues to evolve, so too must our approaches to securing personal data and maintaining user trust.